LLHOST
New Member
LLHOST INC. is an European company established in 2017 by engineers with 10+ years of hosting, network, and development industries experience. The range of LLHOST INC. services is:
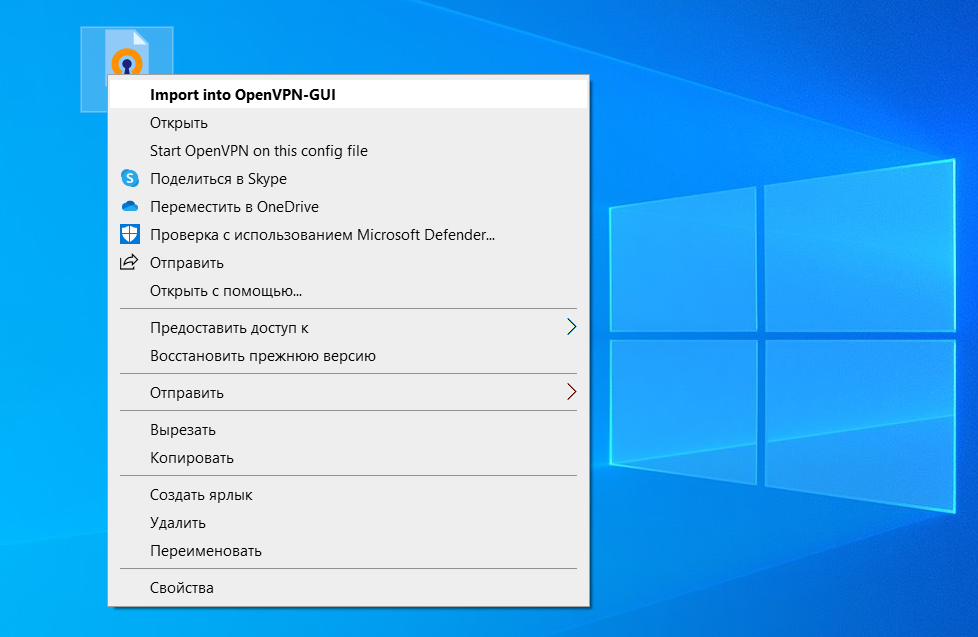
Private VPN Server is a private server for any purpose with a configured VPN.
VPN specs and pricing:
PVS-NL: 100 mbps unmetered, No-logs policy - from $2.24/mo
PVS-PL: 100 mbps unmetered, No-logs policy - from $2.24/mo
PVS-USA:100 mbps unmetered, No-logs policy - from $2.24/mo
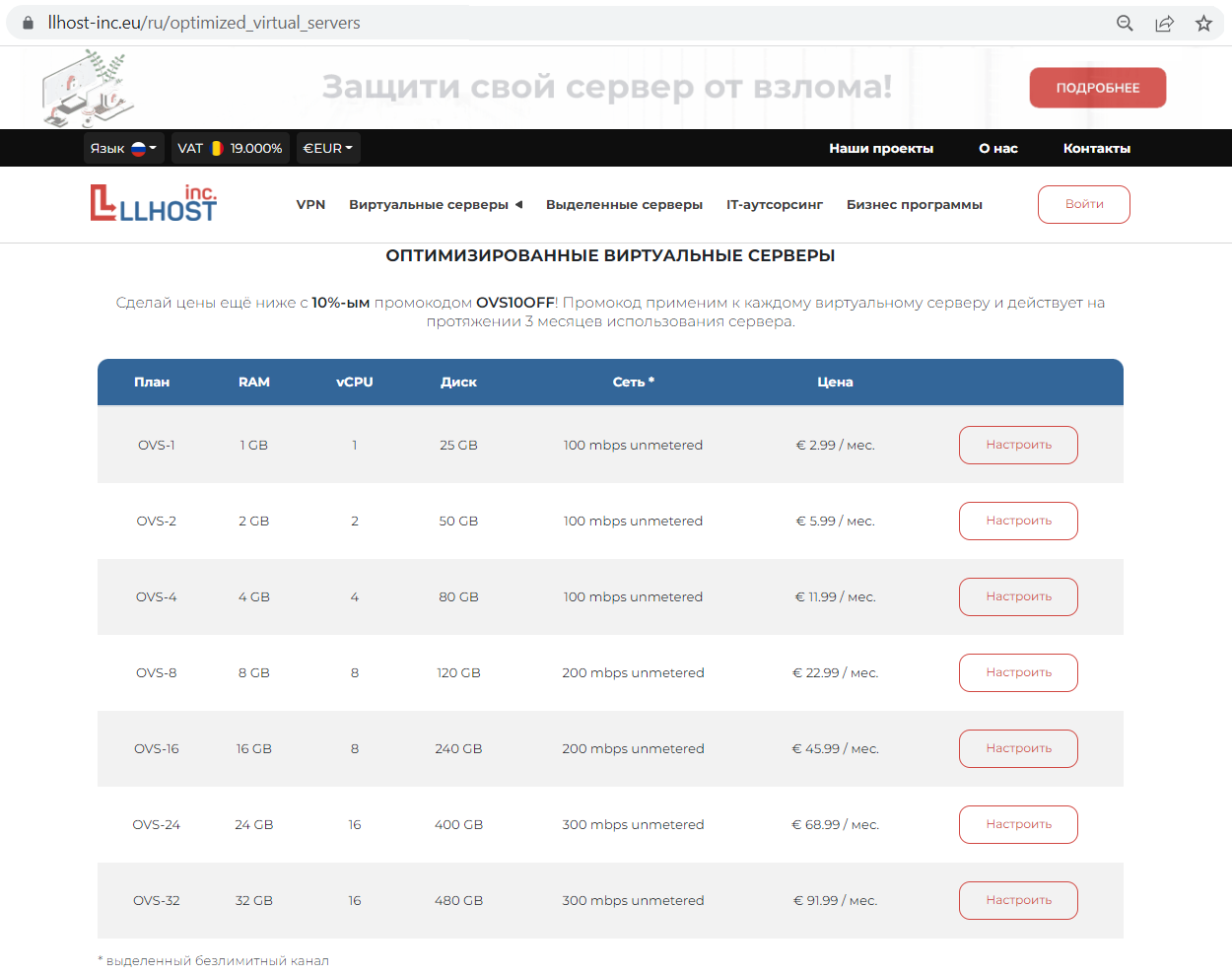
OVS (Optimized Virtual Servers) is a bunch of LLHOST INC. VPS based on KVM virtualization could be used for most common tasks.
OVS specs and pricing:
OVS-1: 1 GB RAM, 1 vCPU, 25 GB SSD, 100 mbps unmetered - €2.99/mo
OVS-2: 2 GB RAM, 2 vCPU, 50 GB SSD, 100 mbps unmetered - €5.99/mo
OVS-4: 4 GB RAM, 4 vCPU, 80 GB SSD, 100 mbps unmetered - €11.99/mo
OVS-8: 8 GB RAM, 8 vCPU, 120 GB SSD, 200 mbps unmetered - €22.99/mo
OVS-16: 16 GB RAM, 8 vCPU, 240 GB SSD, 200 mbps unmetered - €45.99/mo
OVS-24: 24 GB RAM, 16 vCPU, 400 GB SSD, 300 mbps unmetered - €68.99/mo
OVS-32: 32 GB RAM, 16 vCPU, 480 GB SSD, 300 mbps unmetered - €91.99/mo
Get a 30% discount with the promo code “OVS30OFF”!
This discount is available for any plan and is valid for the first 3 months of the billing cycle. It can be activated by an unlimited number of users.
Also, for the long-term projects, we’ve prepared a great offer! A permanent discount depending on the billing cycle:
15% OFF on 3 months payment
20% OFF on 6 months payment
25% OFF on 12 months payment
Each server plan includes:
Our locations:
The Netherlands: Iron Mountain AMS-1 (J.W. Lucasweg 35, Amsterdam, NH, 2031 BE, NL).
Poland: 4 Data Center, (Adamskiego 7, Katowice, PL, 40-069).
The USA: Hurricane Electric Fremont 2 (48233 Warm Springs Blvd, Fremont, CA, USA, 94539).
Our advantages:
Our contacts:
Website: https://llhost-inc.eu/en
E-mail: [email protected]
Send a request to Sales Department
Facebook | LinkedIn | Telegram
Registered office: str. Dr. Petre Herescu 12, parter, cam. 2 București, Sector 5, România
Follow our thread, as you can find all the news, educational materials, and discounts on LLHOST INC. products.
- Virtual, Dedicated, VPN servers in Europe and USA as our main product;
- Internet exchange and network services;
- outsourcing and outstaffing of system administration and development teams.
Private VPN Server is a private server for any purpose with a configured VPN.
VPN specs and pricing:
PVS-NL: 100 mbps unmetered, No-logs policy - from $2.24/mo
PVS-PL: 100 mbps unmetered, No-logs policy - from $2.24/mo
PVS-USA:100 mbps unmetered, No-logs policy - from $2.24/mo
OVS (Optimized Virtual Servers) is a bunch of LLHOST INC. VPS based on KVM virtualization could be used for most common tasks.
OVS specs and pricing:
OVS-1: 1 GB RAM, 1 vCPU, 25 GB SSD, 100 mbps unmetered - €2.99/mo
OVS-2: 2 GB RAM, 2 vCPU, 50 GB SSD, 100 mbps unmetered - €5.99/mo
OVS-4: 4 GB RAM, 4 vCPU, 80 GB SSD, 100 mbps unmetered - €11.99/mo
OVS-8: 8 GB RAM, 8 vCPU, 120 GB SSD, 200 mbps unmetered - €22.99/mo
OVS-16: 16 GB RAM, 8 vCPU, 240 GB SSD, 200 mbps unmetered - €45.99/mo
OVS-24: 24 GB RAM, 16 vCPU, 400 GB SSD, 300 mbps unmetered - €68.99/mo
OVS-32: 32 GB RAM, 16 vCPU, 480 GB SSD, 300 mbps unmetered - €91.99/mo
Get a 30% discount with the promo code “OVS30OFF”!
This discount is available for any plan and is valid for the first 3 months of the billing cycle. It can be activated by an unlimited number of users.
Also, for the long-term projects, we’ve prepared a great offer! A permanent discount depending on the billing cycle:
15% OFF on 3 months payment
20% OFF on 6 months payment
25% OFF on 12 months payment
Each server plan includes:
- 100 mbps Internet channel
- Unlimited bandwidth
- Free/64 IPv6 (for VPS) and IPv4 (for VPN)
- Instant deployment
- User-friendly control panel with embedded popular scripts and images
- Free migration assistance
- 24/7 prompt technical support (response time: 5-10 min max.)
Our locations:
The Netherlands: Iron Mountain AMS-1 (J.W. Lucasweg 35, Amsterdam, NH, 2031 BE, NL).
Poland: 4 Data Center, (Adamskiego 7, Katowice, PL, 40-069).
The USA: Hurricane Electric Fremont 2 (48233 Warm Springs Blvd, Fremont, CA, USA, 94539).
Our advantages:
- 24/7/365 technical support is provided in English and Russian languages.
- Any e-tools and cards from every nook of the world are accepted for payment: bank payment, credit and debit cards, cryptocurrencies, Webmoney, PayPal, Qiwi, LAVA, Ю-MONEY.
- Any plan can be customized upon request, considering individual solutions and configurations.
- Prices and prepayments are fixed. No additional charges for traffic, volumes, speed, etc. excess.
- Any individual conditions, such as discount, term, partnership, etc. can be negotiated on a case-by-case basis.
Our contacts:
Website: https://llhost-inc.eu/en
E-mail: [email protected]
Send a request to Sales Department
Facebook | LinkedIn | Telegram
Registered office: str. Dr. Petre Herescu 12, parter, cam. 2 București, Sector 5, România
Follow our thread, as you can find all the news, educational materials, and discounts on LLHOST INC. products.